- Home
- Technical Products
Enterprise Cloud IT Solutions
Industrial Measurement
- Solutions
- Latest Articles
- About Us
 EN
EN
Designed for Equipment Manufacturers and Operators
ONEKEY Firmware Security Compliance Platform
Efficiently manage network security and compliance of products
Your centralized solution for SBOM authentication, vulnerability detection and prioritization, zero-day exploit discovery, regulatory compliance, and full product lifecycle monitoring. Comprehensive coverage of the entire software development lifecycle (SDLC) helps you build secure products, comply with industry standards, intelligently defend against attacks, and realize an automated security closed loop.
The Consensus Choice of Industry Leaders
State-of-the-art Technology × Expertise Dual Engine Drive
Operational thresholds
A user-friendly interface for development teams, Product Safety Incident Response Teams (PSIRTs), and product managers saves time and reduces costs at the click of a mouse.
Full Process Coverage
From product design to decommissioning and maintenance, all network security and compliance needs are met by one platform.
Specialist Escort
More than just a tool, take advantage of the expertise of our world-leading penetration testing specialists - who also developed the platform and are ready to consult with you.
Functional features designed to minimize risk and effort
End-to-end platform to simplify security processes and ease compliance
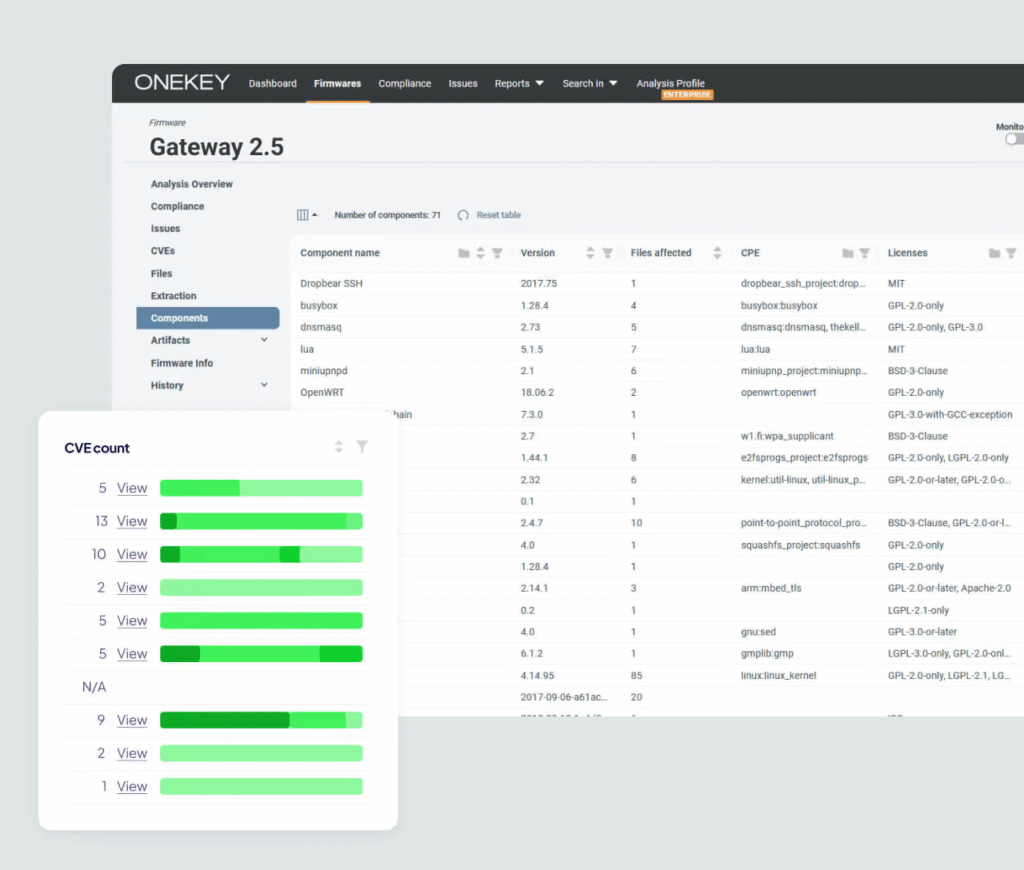
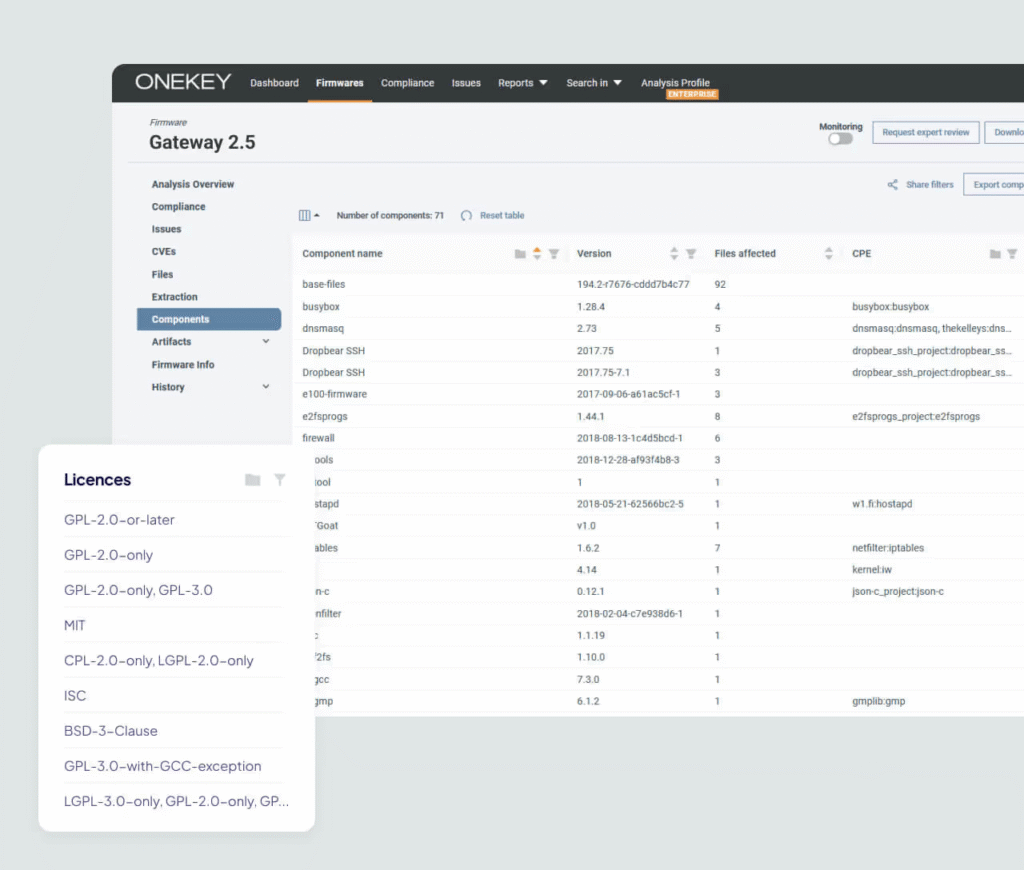
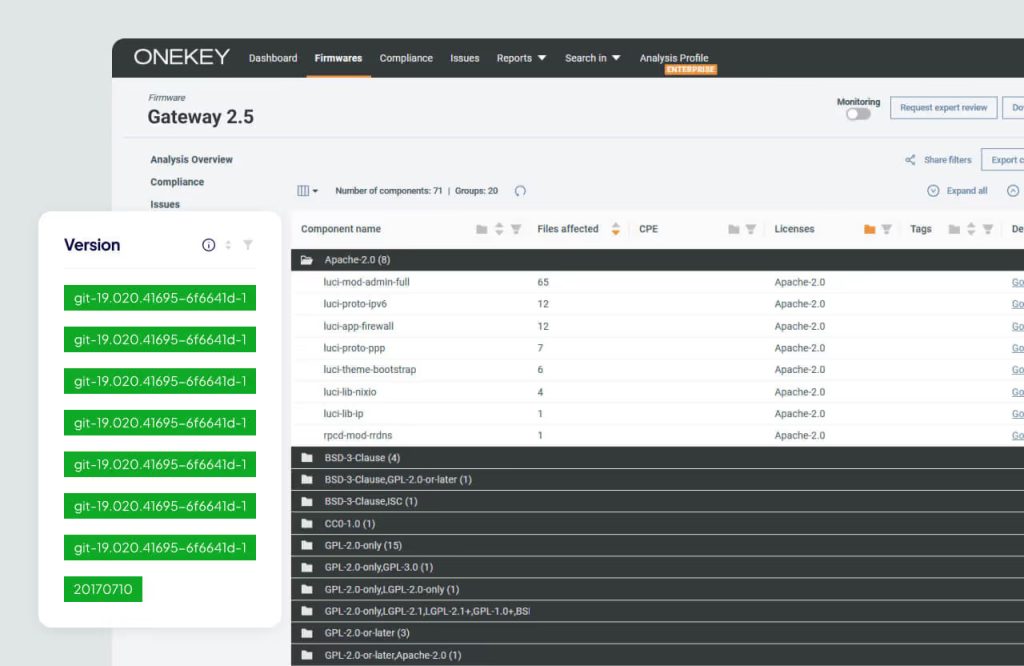
Software Bill of Materials (SBOM) Management
Automated Software Supply Chain Security
- Quickly generate, import and monitor SBOM files, supporting standard formats such as CycloneDX, with one-click export.
- Supports importing component information from binary image files, source code scanners, or integrating third-party data.
- SBOM files can be uploaded independently without source code.
- The platform automatically monitors new and old vulnerabilities around the clock.
Automation Vulnerability Analysis
Significantly shortens the repair cycle
- Automatically scanning the entire product line for new threats 24/7
- Intelligently mark critical vulnerabilities and prioritize resources for remediation.
- Periodic automated assessment and continuous improvement of the safety protection system
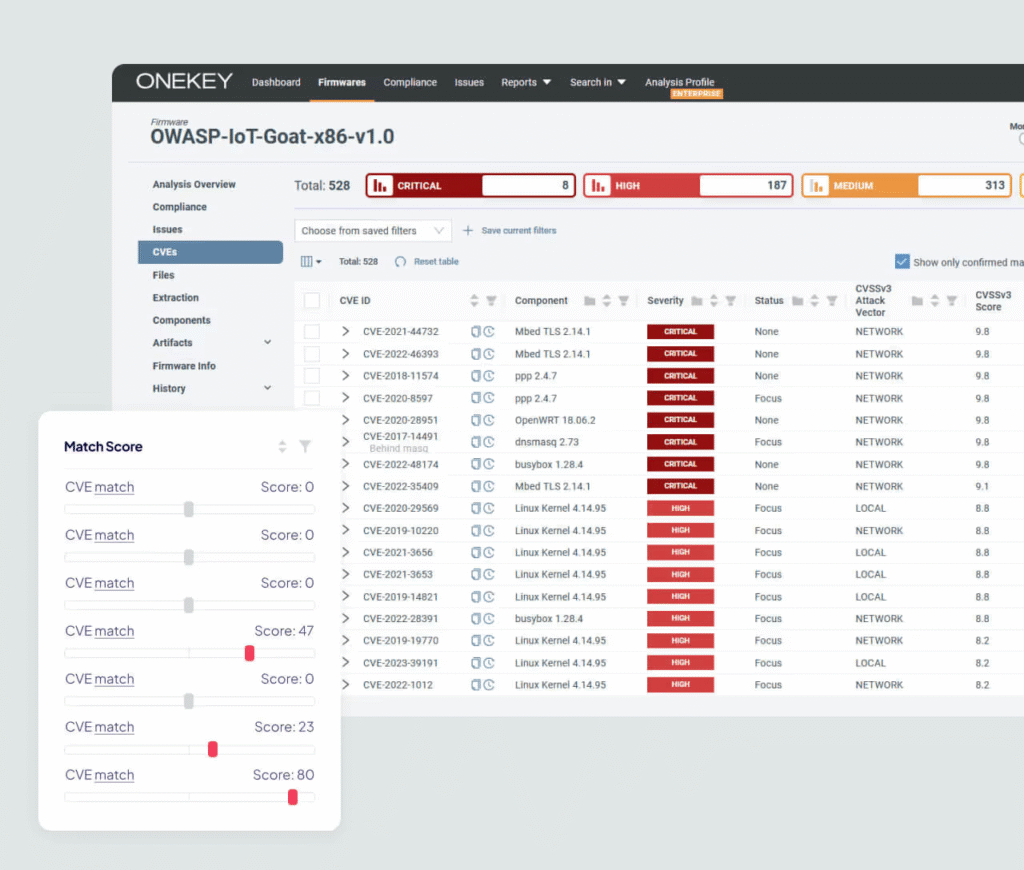
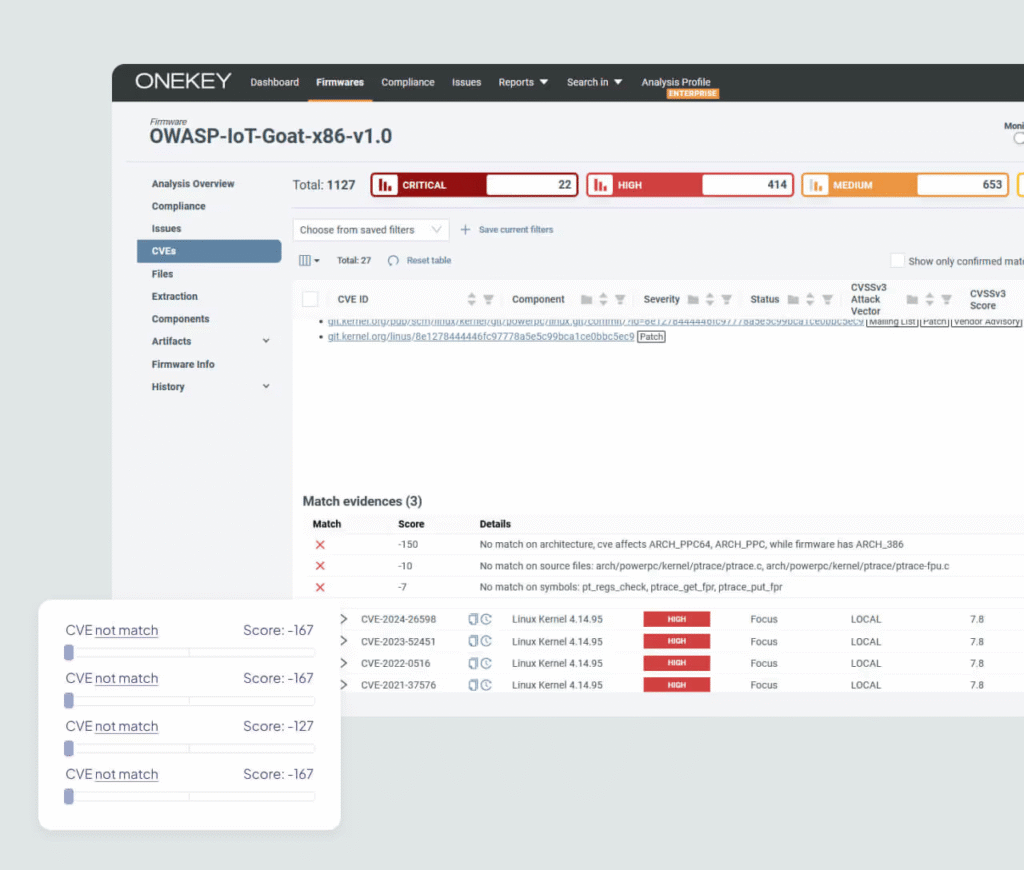
Automated Impact Assessment
Focus on Critical Vulnerabilities
- Thousands of CVE vulnerabilities handled at minute speeds
- Analyze the actual impact of vulnerabilities when combined with the firmware environment.
- Automatically collects evidence and generates visual reports
- Provide an intuitive vulnerability matching scoring system
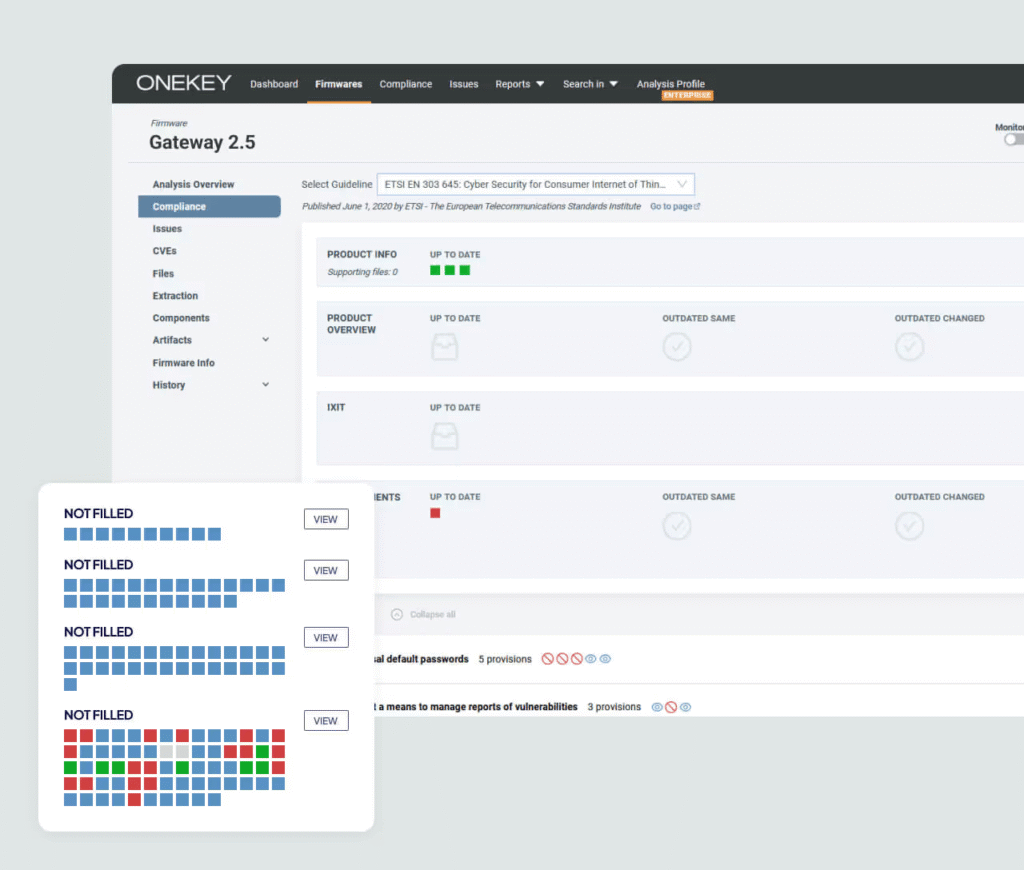
Product Network Security Compliance
Easy compliance
- Proprietary technology Compliance Wizard™ wizard-style guidance:
- EU Cyber Resilience Act (CRA)
- IEC 62443 Industrial Standard
- ETSI 303 645 Internet of Things Specification
- Automated Compliance Analysis and Documentation
- Customizable evaluation templates and audit trails
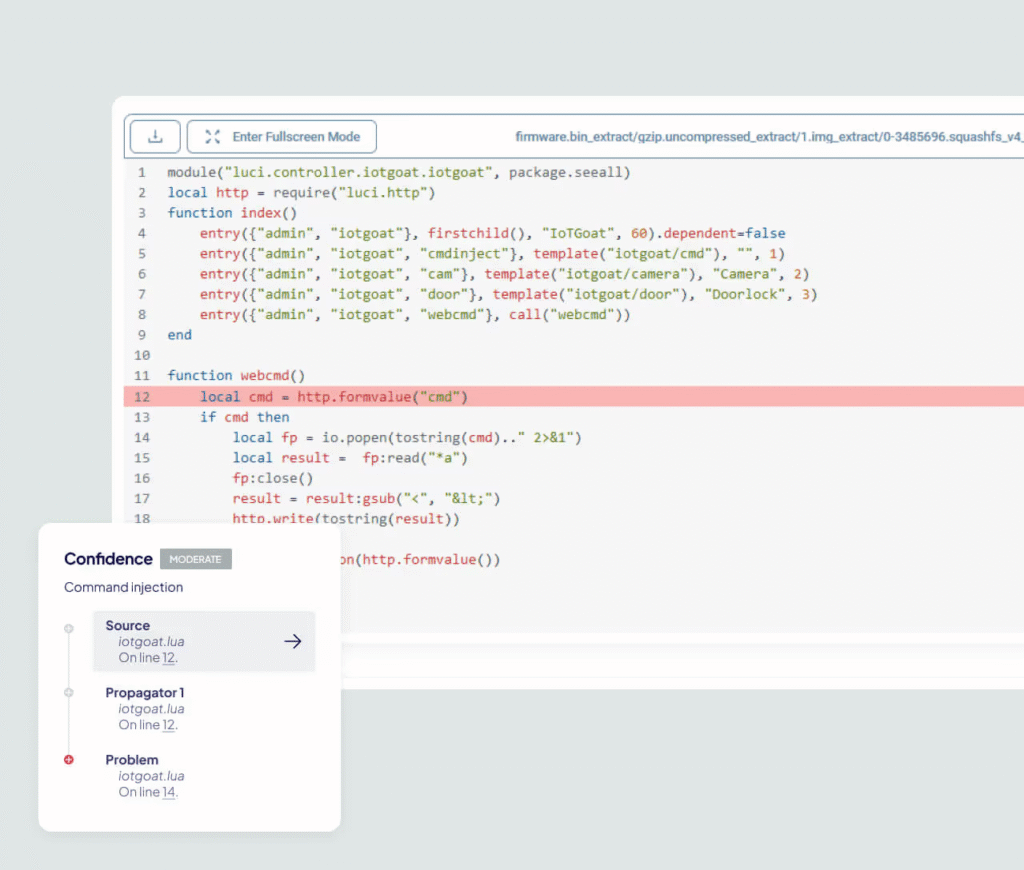
Zero-Day Vulnerability Detection
Discovering Unknown Threats to IoT/OT
- Intelligent Device and Industrial Control System Specialized Detection
- Identify vulnerabilities such as command injection, unsafe communications, etc.
- Static code analysis to track data flow
- Quickly locate potential security risks
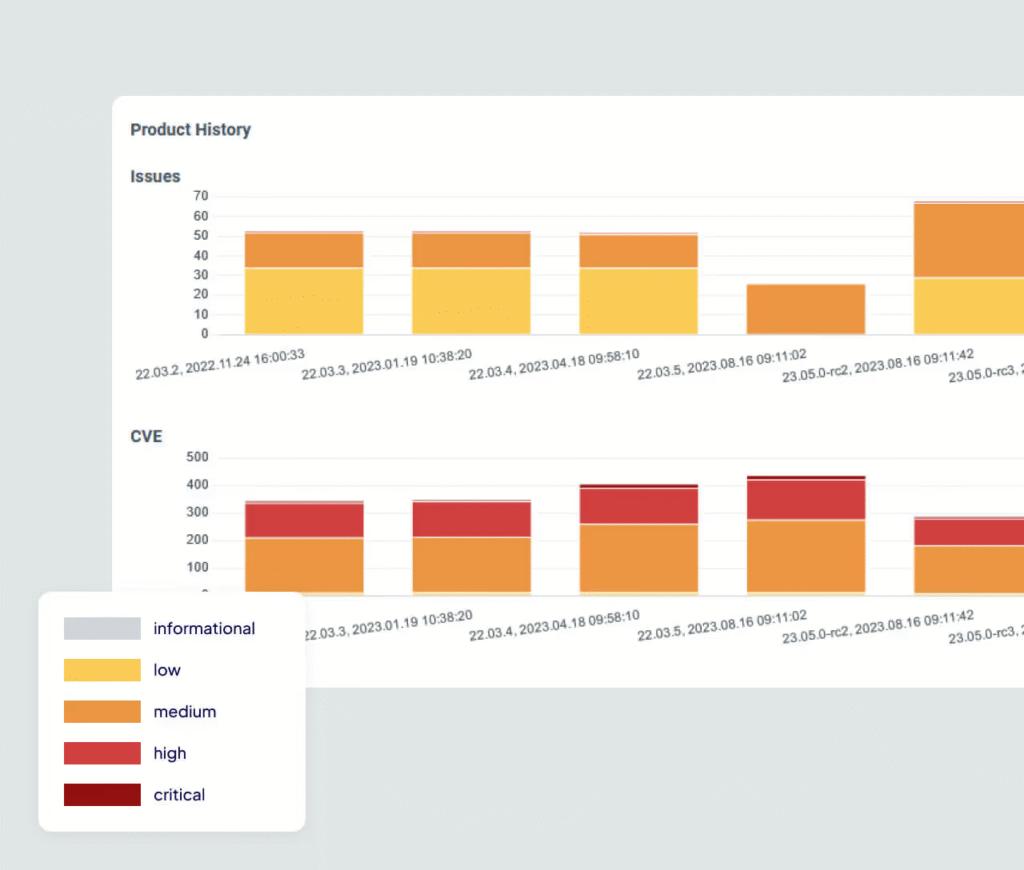
Firmware Security Monitoring
Real-time Risk Scanning
- Daily automatic reanalysis of firmware
- Continuously updated vulnerability database
- Immediate warning of major risks
- Comprehensive tracking of safety improvement history
Open Source License Testing
Avoiding Legal Risks
- Quickly Identify License Conflicts
- Automated Compliance Audit
- Complete Chain of Evidence for Litigation
- Accurate license management records
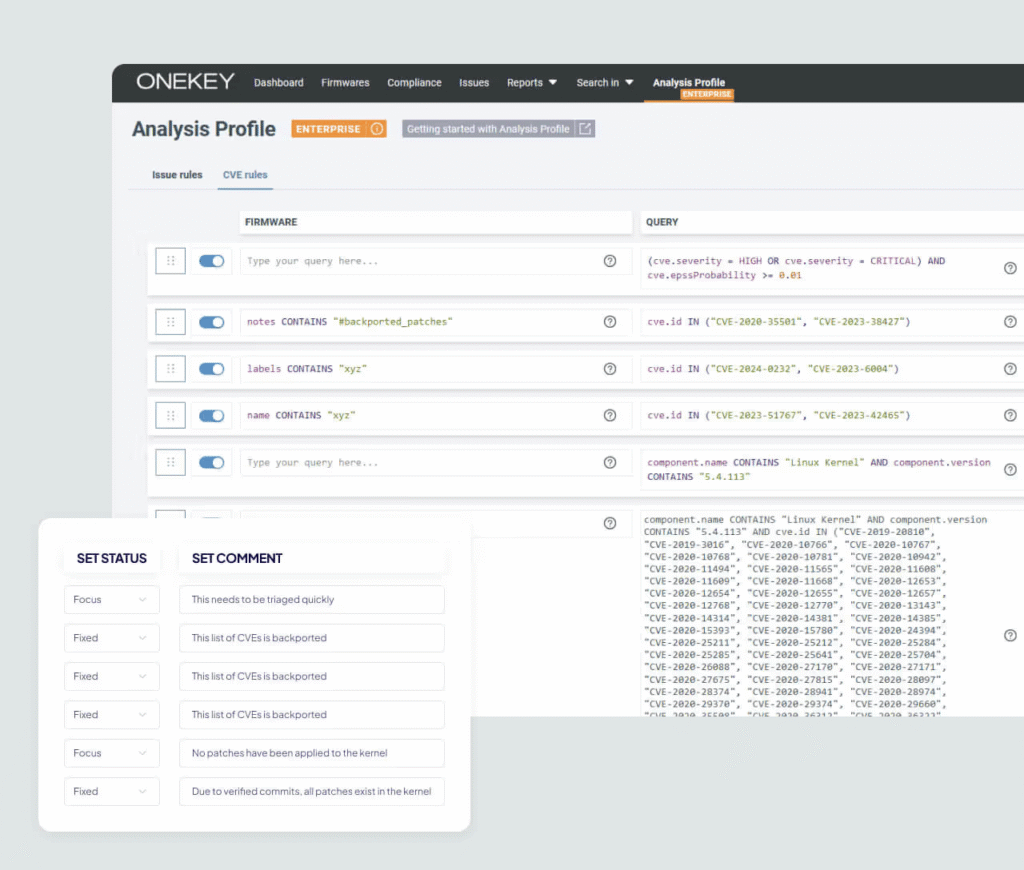
Custom Analysis Settings
Flexible Threat Modeling
- Personalized Threat Rule Integration
- CVE Priority Management
- False alarm filtering mechanism
- Customized risk acceptance thresholds
- Seamless integration with existing security policies
Seamlessly integrate your workflow
Streamline cybersecurity workflows and achieve compliance goals with the ONEKEY end-to-end platform

Azure Entra ID
Supports all OpenID Connect-compliant identity providers, enabling single sign-on (SSO)

Jenkins
Integration of Automated Quality Control in CI/CD Process Scheduling Tools
Splunk
Automated Threat Detection and Work Order Creation via SIEM Tools

Power BI
Sharing dashboard and KPI data with stakeholders

Jira
Create tasks directly in the work order system, project management and collaboration tools.


GitLab/GitHub/Bitbucket etc.
Upload firmware and query analytics through DevOps tools
Customer Testimonials
"ONEKEY has become a core tool in our application safety and compliance management. By continuously automating our security assessments, we not only increase the transparency of our clients' projects, but also ensure compliance with EU CRA regulations. Real-time insights also enable us to provide clear and actionable product safety recommendations to our customers."

"ONEKEY's automated binary analysis technology dramatically improves the efficiency of product security management, increasing the vulnerability detection rate by 3 times while reducing 70% manual operations. The expert team escorted the whole process, making the system connection smooth and unhindered."

"Working with ONEKEY has been an eye-opening experience and their expertise in the security field far exceeds expectations."

"We use ONEKEY's automated firmware analysis technology to provide our customers with a full lifecycle security monitoring service that achieves industry-leading service quality while ensuring efficiency."

"ONEKEY's automated capabilities for detecting critical vulnerabilities in embedded devices have allowed us to focus our manual testing resources on business logic validation, increasing overall security testing efficiency by 40‰."

"Through ONEKEY's pre-release security review, all software releases are rigorously tested before going live to ensure that the security of new feature interfaces is fully protected."

Frequently Asked Questions
Get detailed answers about securing Internet products.
How do you ensure that your product remains safe throughout its life cycle?
With the ONEKEY platform, you get full-cycle protection from development to retirement. Our solution provides continuous monitoring, automated vulnerability detection and regular updates to protect against emerging threats, ensuring that your products are reliably protected at every stage.
Why a Centralized Cybersecurity and Compliance Platform is Necessary
Adopting a unified platform such as ONEKEY significantly optimizes your safety and compliance workflow. This means fewer manual operations, lower operating costs, and a clearer, more intuitive overview of the security status of your products. You'll be able to respond to security threats faster and ensure that your products always meet the latest security standards.
How to integrate network security policies into existing development processes?
ONEKEY integrates seamlessly with development tools such as GitLab, Jenkins, Jira and more. By embedding automated security checks into existing workflows, you can find and fix vulnerabilities early in the development process without the burden of additional work, ensuring an efficient and secure development process.
What are the advantages of automated product safety?
Automation technology dramatically reduces manual operations, saves time and lowers error rates. ONEKEY allows your team to focus on core business by automating vulnerability assessment, compliance checking and threat detection. It not only improves your overall security level, but also helps you respond more quickly to various security risks.
How do you ensure that your products always meet the latest safety standards?
ONEKEY's unique Compliance Wizard™ feature keeps track of the latest developments in relevant network security standards. It helps you quickly identify new regulatory requirements and adapt them with minimal adjustment costs. With automated change alerts, compliance management is simple and efficient.
Professional technical support from HONGKEI to help you succeed in your project.
As a provider specializing in machine vision and optoelectronic inspection solutions, Avision is also committed to providing you with a range of paid technical services related to this product, aiming to help you succeed in your project in the most cost-effective way. Please contact us if you need technical services related to this product!

