(i)CRA Full Process Compliance Assessment
Automated assessment against CRA regulatory requirements, including product risk level, security documentation, vulnerability management, supply chain security, incident response, etc., and output of compliance gap reports, so that enterprises can clearly grasp "where they are out of compliance and how to improve".
(ii) Fully automated SBOM generation and management
Generate complete SBOMs directly from firmware binary with support for standard formats such as SPDX and CycloneDX, solving the CRA-mandated issue of supply chain transparency and avoiding compliance denials due to unknown components.
(iii) Firmware Depth Vulnerability Detection
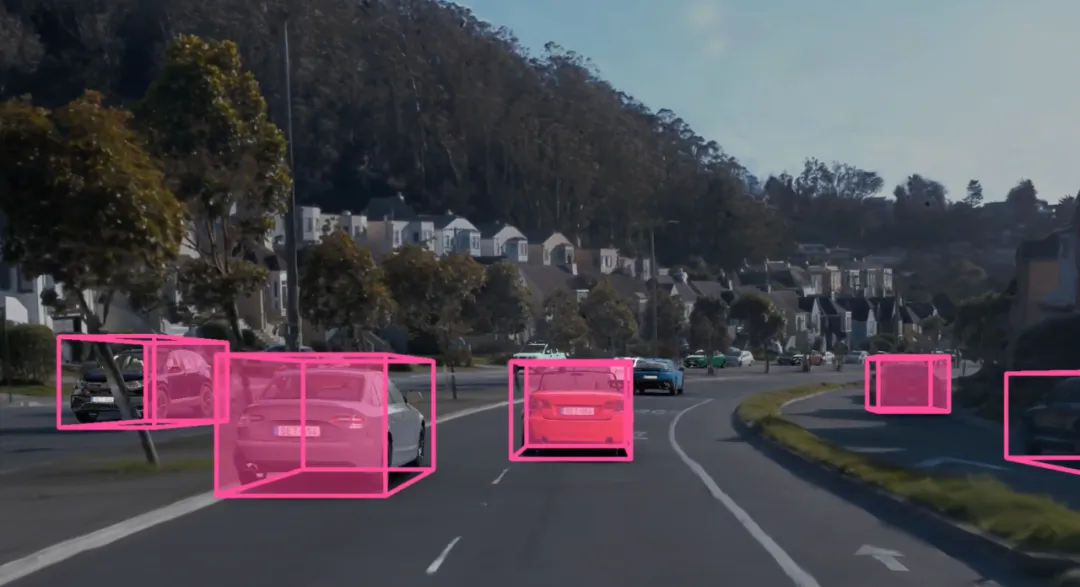
Supports PNG detection and recognition:
Known CVE Vulnerabilities
Weak code, hard-coded gold key
Unsecure Communication Settings
Risks of unauthorized access, debugging port opening, etc.
Meet the CRA's mandatory requirements for vulnerability discovery, handling, and reporting.
(iv) Automatic generation and retention of compliance evidence
Automatically generates audit logs, detection reports, rectification records and evidence packages to meet CRA's requirements for traceability and certifiability, making it easier to respond to regulatory spot checks.